What is IP security overview and architecture?
What is IP security overview and architecture?
The IP security architecture (IPsec) provides cryptographic protection for IP datagrams in IPv4 and IPv6 network packets. This protection can include confidentiality, strong integrity of the data, data authentication, and partial sequence integrity. Partial sequence integrity is also known as replay protection.
What is IP security overview?
IP security allows individual users or organizations to secure traffic for all applications, without having to make any modifications to the applications. Therefore, the transmission of any data, such as e-mail or application-specific company data, can be made secure.
What is ISO security architecture?
2 ISO SECURITY SERVICES The Security Architecture of the OSI Reference Model (ISO 7498-2) considers five main classes of security services: authentication, access control, confidentiality, integrity and non-repudiation.
How many components are there in IP security architecture?
The design includes three components: (1) a security policy for determining when, where, and how security measures are to be applied; (2) a modular key management protocol, called MKMP, for establishing shared secrets between communicating parties and meta-information prescribed by the security policy; and (3) the IP …
What is IP security architecture DOI?
DOI (Domain of Interpretation): DOI is the identifier which support both AH and ESP protocols. It contains values needed for documentation related to each other.
What are the benefits of IPsec?
IPsec delivers the following benefits:
- Reduced key negotiation overhead and simplified maintenance by supporting the IKE protocol. IKE provides automatic key negotiation and automatic IPsec security association (SA) setup and maintenance.
- Good compatibility.
- Encryption on a per-packet rather than per-flow basis.
What are the applications and benefits of IP security and explain the architecture of IP security?
IPsec provides the following security services for traffic at the IP layer: Data origin authentication—identifying who sent the data. Confidentiality (encryption)—ensuring that the data has not been read en route. Connectionless integrity—ensuring the data has not been changed en route.
What is security architecture design?
Security architecture and design looks at how information security controls and safeguards are implemented in IT systems in order to protect the confidentiality, integrity, and availability of the data that are used, processed, and stored in those systems.
What are the applications of IP security?
To encrypt application layer data. To provide security for routers sending routing data across the public internet. To provide authentication without encryption, like to authenticate that the data originates from a known sender.
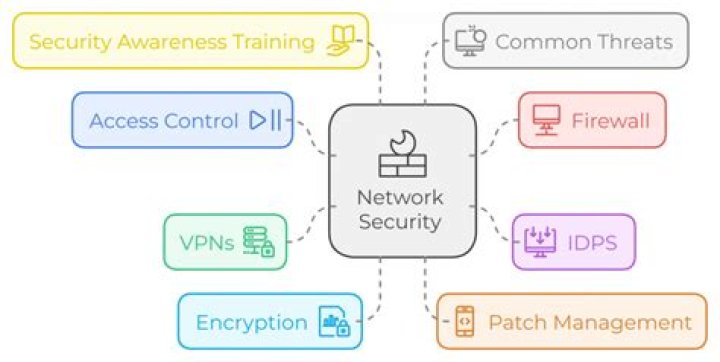
What are the 3 major components of IPsec?
IPSec Components
- Encapsulating Security Payload (ESP): Provides confidentiality, authentication, and integrity.
- Authentication Header (AH): Provides authentication and integrity.
- Internet Key Exchange (IKE): Provides key management and Security Association (SA) management.