What is information security in general?
What is information security in general?
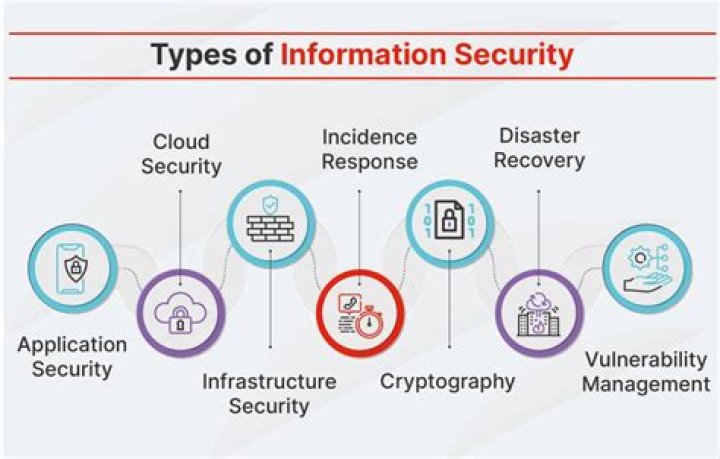
Information Security is basically the practice of preventing unauthorized access, use, disclosure, disruption, modification, inspection, recording or destruction of information. Information Security programs are build around 3 objectives, commonly known as CIA – Confidentiality, Integrity, Availability.
What is DLP used for?
Data loss prevention (DLP) is an approach that seeks to improve information security and protect business information from data breaches. It prevents end-users from moving key information outside the network. DLP also refers to tools that enable a network administrator to monitor data accessed and shared by end users.
What does Digital Guardian agent do?
Digital Guardian Endpoint Data Loss Prevention gives you the broadest coverage and control, including Windows, macOS, and Linux endpoints. The DG agent captures and records events at the system, user, and data level, both when connected to the corporate network, or offline.
What is the first step in information security?
Planning and Organization The first step in an effective information security framework is to understand what exactly your organization is trying to protect. You can start by thoroughly mapping out your network.
What is DLP McAfee?
McAfee DLP Prevent allows you to reduce risks associated with your data and enables you to take a variety of remediation actions, including encrypting, redirecting, quarantining, and blocking to support your compliance with regulations governing the privacy of sensitive information.
What is DLP office365?
Data loss prevention (DLP) helps you prevent the unintentional or accidental sharing of sensitive information. DLP examines email messages and files for sensitive information, like a credit card number. Display a warning to the end user who is sending the email or sharing the file.
What is Proofpoint DLP?
Proofpoint Enterprise Data Loss Prevention (DLP) is the only people-centric DLP solution that brings context across content, behavior and threats together for people-centric insight into and prevention of data loss.
What are the 5 steps of the information security Program Lifecycle?
This process is outlined in detail in the following sections.
- Step 1: Identify. The first step in the information security program lifecycle is to identify what items need to be protected.
- Step 2: Assess.
- Step 3: Design.
- Step 4: Implement.
- Step 5: Protect.
- Step 6: Monitor.

