What is buffer overflow vulnerability?
What is buffer overflow vulnerability?
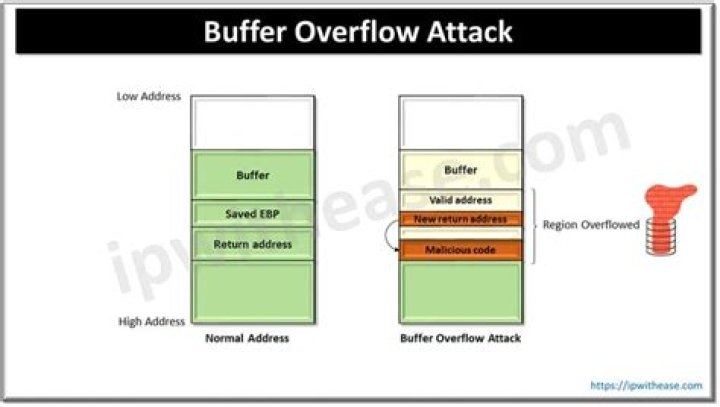
A buffer overflow vulnerability occurs when you give a program too much data. The excess data corrupts nearby space in memory and may alter other data. As a result, the program might report an error or behave differently. Such vulnerabilities are also called buffer overrun.
What are the problems with buffer overflow?
Buffer overflows can affect all types of software. They typically result from malformed inputs or failure to allocate enough space for the buffer. If the transaction overwrites executable code, it can cause the program to behave unpredictably and generate incorrect results, memory access errors, or crashes.
What are the types of buffer overflow attack?
There are two types of buffer overflows: stack-based and heap-based. Heap-based, which are difficult to execute and the least common of the two, attack an application by flooding the memory space reserved for a program.
What are three unsafe C functions in buffer overflow?
That is why the safest basic method in C is to avoid the following five unsafe functions that can lead to a buffer overflow vulnerability: printf , sprintf , strcat , strcpy , and gets .
How does buffer overflow vulnerability occur?
A buffer overflow, or buffer overrun, occurs when more data is put into a fixed-length buffer than the buffer can handle. This overflow usually results in a system crash, but it also creates the opportunity for an attacker to run arbitrary code or manipulate the coding errors to prompt malicious actions.
What is heap buffer overflow?
A heap overflow condition is a buffer overflow, where the buffer that can be overwritten is allocated in the heap portion of memory, generally meaning that the buffer was allocated using a routine such as malloc(). For example, object methods in C++ are generally implemented using function pointers.
What is a buffer overflow and how is it used against a Web server?
A buffer overflow occurs when a program tries to write too much data in a fixed length block of memory (a buffer). Buffer overflows can be used by attackers to crash a web-server or execute malicious code.
What is meant by marketplace for vulnerability?
A market consisting of vulnerable consumers. A market to sell and purchase vulnerabilities.
Which string library functions is unsafe for buffer?
// copying src into dest. Problem with strcpy(): The strcpy() function does not specify the size of the destination array, so buffer overrun is often a risk. Using strcpy() function to copy a large character array into a smaller one is dangerous, but if the string will fit, then it will not be worth the risk.
What are unsafe functions in C?
Unsafe Functions
| UNSAFE | Safer alternative |
|---|---|
| gets | fgets |
| strcat | strncat |
| strcpy | snprintf |
| sprintf | snprintf |
What is a buffer in buffer overflow?
Definition of a Buffer Overflow A buffer is a sequential section of memory allocated to contain anything from a character string to an array of integers. A buffer overflow, or buffer overrun, occurs when more data is put into a fixed-length buffer than the buffer can handle.